Read:
Kill switches are originally intended for use as a remote method of wiping data off a smart device remotely. But history has shown that if you have a kill switch installed, if discovered by hostile parties can be used against you. If an attacker manages to find a way to send the correct command to activate the kill switch, it might disrupt or even endanger whomever owns this kill switch (imagine if you were to plant a remote kill switch into smart devices and these smart devices have some sort of link to life support systems for health patients, that would be really dangerous).
Remote wiping implementations are not so straightforward in it's designs and implementations. One have to consider the fields of economics, politics, social behaviours and most importantly, the technical side of computer security.
Relating to the technical side of computer security, some remote wipe providers may offer some form of strong symmetric key or PKI infrastructure to encrypt the communication between your smart phone and the remote command tool to send the kill signal, but what is going to protect these encryption keys or passwords from falling into the wrong hands ?
Once you have given someone the access to remotely send commands to your own system, you have effectively lost control over your system. That is the basis of computer security: which is to secure your system and prevent yourself from losing control.
For the economical, social and political side of matters, who truely owns the smart device ? Is the person who bought and signed the contract for the smart device the true owner of the device ? Are there political motivations for inserting political and governmental backdoors via the remote kill switch ? Are the service providers and software providers trying to gather more user data some mechanism in the remote kill switch for their own benefits ? There are much more to consider than the outright "benefit" of simply remote wiping your smart devices if it lands in the wrong hands.
Who would know if some malicious employees or someone within the the company or organization whom you have given remote wipe command access to might not intentionally or accidentally wipe your smart device or use the security loophole(s) of the remote kill switch to remote control your smart device ?
An alternative to using a blackbox style remote kill switch which you have no access or control over the source codes and mechanisms is to look for open source alternatives which you can review the source codes to ensure that there are no backdoors in the remote kill switch and the mechanisms in place to transfer the command to remotely kill a device is sent our via secure and conscious means. The problem with such an open source implementation is not everyone knows about computer security and how to evaluate codes to ensure that the codes and kill switch mechanics are safe. People are likely to simply purchase or subscribe to a kill switch without proper inspection and trust it which can be detrimental to one's own privacy and security.
In essence, deliberately introducing a loophole (remote kill switches are considered a deliberate loophole in CS field) into a system degrades it's overall security regardless of the intention or purpose.
Here are a few tips to secure your smart devices:
- Never leave them on the table or chair or leave them unattended even for a few minutes if these devices contain personal data (phone contacts, email, address book, PIN managers, bank transaction applications ... etc).
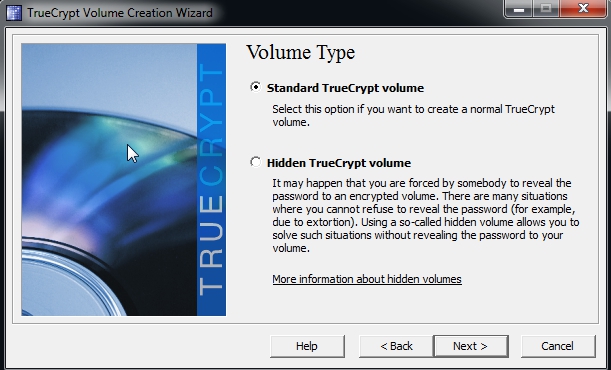
- Filesystem / Volume encryption.
- Always use a Password Manager with a Master Password and never write them down on paper or Notepad.
- Never share passwords.
Afterall, the best device security is yourself being cautious and aware of the surrounding. Depending on some loophole technology to remote kill your device is the worse idea.